Hacking pro plus s
Kali Linux #hacking #cybersecurity #viral #cyberattackdefense
6 days ago - 0:32

60 Minutes
Defense Against Cyber Attacks and Other Threats | 60 Minutes Full Episodes
11 months ago - 53:38

BrainyXStudios
AI Cyberattack Defense: How it Works
6 months ago - 0:27

Hacked dAily
Fake Cl0p Ransomware Extortion Letters: Outsmart This Latest Cyber Scam Now
3 months ago - 0:35

Learn & Earn
"Web Application Firewall EXPLAINED: Unmasking the Secrets of Cyber Attack Defense!"
10 months ago - 19:07

John Hammond
Can you handle a cyber attack? TryHackMe SOC Simulator
4 months ago - 20:06

Cyber Attack - Defense
Siber güvenlik alanında kendimi geliştirmek isteyen, aynı zamanda Bilgisayar Programcılığı okuyan bir öğrenciyim. 20 yaşındayım ...
@CyberAttack-Defense subscribers

IFoxProjects
Adaptive Deep Reinforcement Learning Algorithm for Distribution System Cyber Attack Defense With Hig
4 months ago - 2:40
MyGenieNetwork LLC
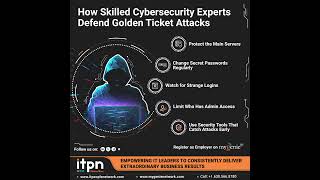
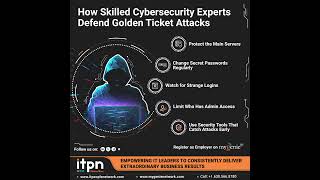
Golden Ticket Attacks can give hackers full control of your network.
1 month ago - 0:30

KeepItTechie
DOE Academic Grants | Developing Cyber Attack Defense Tools
3 years ago - 10:27

RaviTeja Mureboina
The Invisible Hack #hack #technews #news #cyberattack #cyberattacks #cyberattackdefense #trend
5 months ago - 0:39

Inspire Tech daily
Cyber Heroes: Ultimate Virus Battle and Cyber Attack Defense!
9 months ago - 2:32

Apna Shakil
Cyber attack in India #Cyberattack #IndiavsPakistan #war #cyberattackdefense
2 months ago - 0:34

PlokenV
DeepSeek AI Cyber attack Defense 🤯 #shorts #edit #trollfaceedit #deepseek #tech #ai #china #chatgpt
5 months ago - 0:20

info Crater
Cyber attack | change password #cyberatack#cybernews#earnmoneyonline #tranding
1 month ago - 1:20

Cyber_Security.
00027 4 1 Understanding Passive vs Active Reconnaissance
4 months ago - 2:55

Bitten Tech
Red Teamer VS Ethical Hacker #shorts
8 months ago - 0:44

VDRGurusOnCloud
Fortify Your Business: Cyberattack Defense and Recovery Strategies | VDRGurusOnCloud
1 year ago - 3:27

TU
Bluesnarfing: what is this type of Bluetooth attack and how to avoid it? #cybersecurity
1 year ago - 0:26

XOOM PROJECTS
Adaptive Deep Reinforcement Learning Algorithm for Distribution System Cyber Attack Defense With Hig
8 months ago - 0:45

British Army
Cyber Warfare Simulation | Defence Cyber Marvel 3 | British Army
1 year ago - 3:26

Leverage Virtual
Is Hiring a VA a Cyber Security Risk: Confidentiality and Non-disclosure Agreement
10 months ago - 0:59

Kibreab Adane, PhD.
ሳይበር ጥቃትነን ለመከላከል የ ሰው፤ቴክኖሎጂ ና ፖሊሲ ሚና (Cyberattack Defense: The Role of People, Technology, &policy)
10 months ago - 5:21

𝙋𝙧𝙖𝙨𝙖𝙣𝙩𝙝𝘿𝙖𝙞𝙡𝙮𝙄𝙣𝙛𝙡𝙪𝙚𝙣𝙘𝙚
Stay Safe: How Hackers Are Using CAPTCHA to Spread Malware🚨 Beware! Dangerous Clipboard Hijacking
3 months ago - 0:44

DW Urdu اردو
سائبر حملوں سے کیسے بچیں | Cyberattack: Defense training for company bosses
5 years ago - 4:10

Latest News Today
Latest News Today - Community security urged caution about the cyber attack defense
7 years ago - 4:25

black hat
Anonymous #Hacker #Pentester Bug hunter short video
2 years ago - 0:11

Shadow_Secure
The Fortress Falls: Cracking the Uncrackable Network? #cybercertification #coding #onlinesafety
3 weeks ago - 0:27

Threat Intelligence Lab
The Story of The Hacker That Hacked NASA and The Defense Threat Reduction Agency #hacking
1 year ago - 0:52

Bitzze
USA Vs China Military Comparison 2025 || #usa #china #battle #bitzze
1 month ago - 0:06

Copper Digital
Smart Home Security: 7 Must-Do Steps to Keep Hackers away!
2 years ago - 0:34

Security For You
WannaCry attack - NSA connection | Hero Marcus Hutchins was arrested by FBI Full story in video soon
1 year ago - 0:56

CISO Marketplace
IAF Jet Hacked Mid-Air?! India's Defense Nightmare Exposed!
1 month ago - 1:07

Securium solutions
Day 10: Preparing for the Future of Cybersecurity! #Cybersecurity #SecurityPlatforms
4 months ago - 0:40

Cyber_Security.
00027 4 1 Understanding Passive vs Active Reconnaissance
4 months ago - 2:55

Robotwar
대기업 보안팀장 자리에 오른 인공지능 휴머노이드 로봇!AI Humanoid Robot Becomes Head of Corporate Security!
6 days ago - 0:10

Sstoryfyy
The most dangerous cyber crimes.
2 months ago - 0:33

InfoTechSite
Understanding Least Privilege in Data Security MCQ Question #advancedsecurity #cybersecurity #cc
8 months ago - 0:28

Tactical Warfare Experts
What Is DFARS And How Does It Impact DIB Cybersecurity? - Tactical Warfare Experts
1 month ago - 3:14

PatriotMikeCook
The New Era of Cyber Warfare: Defending Against China's Threats
1 year ago - 1:08

Edufinance fusion
Operation Sindhur (Part 3): India’s Silent Strike Plan Leaked?#shorts #shortfeed #war #pmmodi
2 months ago - 0:54

siminsights
MR Cyber Security Interview
1 year ago - 2:33

Pax8
What is a key to being successful? Skill-up your employees and provide upward mobility!
1 year ago - 0:26

TechHacks__
Cybersecurity Myths Busted! #ethicalhackingtraining #cybersecurity #computer #digitalforensics
9 months ago - 0:56

Cyber For You
IPS vs IDS: What's the REAL Difference? Explained! #onlinesafety #technews #securedevice
3 months ago - 0:49

Global Watch Nexus
Protecting Your Business from Cyber Attacks: Essential Tips and Tools
1 year ago - 11:47

KUYA RENE
How to Conduct Security Risk Assessment
1 year ago - 3:05

Lamentomori
💻 Cyber Defense Explained – Protect Your Digital Assets NOW!
4 months ago - 2:08

Cyber Legion
Cyber Legion Revolutionizing Product Security
1 year ago - 3:07

Velocity Technologies
Understanding Ransomware as a Service Risks and Strategies Unveiled
5 months ago - 5:51

SecurityFirstCorp
What Is A Network-Based IPS? - SecurityFirstCorp.com
3 days ago - 3:39

Dwarka Education
Crafting a Trojan: Gaining Access to Target Systems
1 year ago - 7:02

Universal Attack
Ben Universal Attack. Yani Universal Cyber Attack Defense Kanalının Sahibiyim. Bu Kanalda(Kali Linux-Hack, Siber Saldırı, ...
@universalattack subscribers

High Wire Networks
Wetzel & Associates Interview Overwatch Managed Security
Intro ...
4 years ago - 11:54

Doomsday Scenarios
Surviving the Unthinkable: Doomsday Scenario Survival Tips
4 months ago - 1:01

Sonika Sowdari
Impact of Controls on Data Integrity and Information Systems (By Sonika Sowdari)
3 months ago - 4:54

Robotwar
대기업 보안팀장 자리에 오른 인공지능 휴머노이드 로봇!AI Humanoid Robot Becomes Head of Corporate Security!
6 days ago - 0:10

Boundless Accelerator
Toolkit Tuesday Webinar: Demystifying cybersecurity to keep your customers and your business, safe.
3 years ago - 1:16:34

Kirkham IronTech
The 5 Things That WILL Protect Your Company From Cyber Attacks
3 years ago - 5:49

disavowed913
Price Tampering Vulnerability on UrbanCompany
5 months ago - 1:59

Oops_14
Data security : Challenges in different sectors (HNC Level)
5 months ago - 5:24

Hillstone Networks
BFM Interview - Building Zero Day Threat Defense Through Network Security
Intro ...
7 years ago - 20:29

Hacking pro plus s
Ethical hacking complete series Bug Bounty complete series Penetration testing letest tools and there use Hacking ...
@hackingpropluss5199 subscribers

James JR Reeves
James JR Reeves | The Future of Cloud Security
7 months ago - 1:14