Computerphile
Public Key Cryptography - Computerphile
11 years ago - 6:20

Practical Networking
Public and Private Keys - Signatures & Key Exchanges - Cryptography - Practical TLS
3 years ago - 12:33

Ask Leo!
What Is Public Key Cryptography?
2 years ago - 15:26

Khan Academy
Encryption and public keys | Internet 101 | Computer Science | Khan Academy
6 years ago - 6:40

Code Sketched
encryption explained | Public key cryptography
6 years ago - 6:33

Firas Almutar
Symmetric Encryption Functions in MYSQL 1 تشفير البيانات
1 day ago - 5:09

Chirag Bhalodia
Public key cryptography and Application of public key cryptography
4 years ago - 16:03

Intellipaat
Public Key Cryptography | Assymetric Encryption | Cryptography And Network Security | Intellipaat
1 year ago - 11:41

The Helpful Hacker
TryHackMe Public Key Cryptography Basics Walkthrough | Step-by-Step CTF Guide
8 months ago - 56:54

Gate Smashers
Lec-83: Asymmetric key Cryptography with example | Network Security
6 years ago - 8:23

Neso Academy
Public Key Cryptography | Chapter-4 | Cryptography & Network Security | nesoacademy.org
2 years ago - 1:40

Chirag Bhalodia
Application of public key cryptography | Authentication | Confidentiality | Digital Signature
4 years ago - 7:14

Khan Academy Labs
Public key cryptography: What is it? | Computer Science | Khan Academy
11 years ago - 4:32

Android Authority
How does public key cryptography work – Gary explains
8 years ago - 15:46

Cyber Hashira
Cryptography : Public Key Cryptography Standards explained.
2 years ago - 13:00

Ignite Charlotte
Public Key Cryptography - Peter Squicciarini - Ignite Charlotte 3
13 years ago - 5:33

LTnow
Tech Jargon 101 - Public Key Cryptography
6 months ago - 1:00

Sunny Classroom
Public Key Encryption (Asymmetric Key Encryption)
8 years ago - 5:06

edureka!
Public Key Cryptography Decoded | What is Cryptography? | Edureka | Cybersecurity Live - 2
Streamed 4 years ago - 32:22

Neural Nexus
Cryptography #cryptography #trending #trendingshorts #shorts #short #video #viralvideo #viralshort
10 months ago - 0:47

ProsperityPursuits
Quantum Computers: The Secret Threat to Public Key Cryptography
2 years ago - 0:19

Djalil Ayed
🔑🔑🔑 Public Key Cryptography Basics: RSA, SSH, and More in Cyber Security 101 | TryHackMe | SAL1 🔑🔑🔑
9 months ago - 26:33

Stevdza-San
Public-Key Cryptography Explained
1 year ago - 1:01

King Studio
introduction of cryptocurrency / what is cryptography
1 year ago - 0:30

SecurityFirstCorp
How Does Public-Key Cryptography Work? - SecurityFirstCorp.com
6 months ago - 2:44

Neural Nexus
Cryptography and Blockchain #cryptography #blockchain #trending #trendingshort #shorts #short #video
10 months ago - 0:47

Nitrix Tech
Public Encryption Explained in 1 Minute | Cryptography
2 years ago - 0:56

Neural Nexus
Cryptanalysis #cryptography #new #trending #trendingshorts #shorts #short #video #viralvideo #news
10 months ago - 0:43

Almond Consulting
Asymmetric Cryptography: The Key to Your Privacy
8 months ago - 0:48

Neural Nexus
Quantum Cryptography #cryptography #new #trending #trendingshorts #shorts #short #video #viralvideo
10 months ago - 0:44

@affan host
How Public-Key Cryptography Revolutionized Digital Security
2 months ago - 1:07

Datasafe World
Diffie-Hellman Algorithm, Cybersecurity Mini Dictionary #shorts
1 year ago - 0:21

Coinclips
The Role of Cryptography in Cryptocurrency: Explained
11 months ago - 0:33

Prototype Project
DHKE + Python + multiplicative masking encryption
2 years ago - 0:54

t v nagaraju Technical
PRINCIPLES OF PUBLIC KEY CRYPTOGRAPHY || ASYMMETRIC KEY ENCRYPTION -- NETWORK SECURITY
6 years ago - 13:39

Trouble- Free
#27 Principles Of Asymmetric Key Cryptography |CNS|
3 years ago - 7:23

Gloves Off!
A Day in the Life of Cryptography Pioneer Whitfield Diffie
3 months ago - 0:57

nihki prihadi
The Revolutionary Impact of Public Key Cryptography #facts #cryptography #bitcoin
1 year ago - 0:34

Chirag Bhalodia
Requirement of Public Key cryptography | Cryptanalysis of public key cryptography
4 years ago - 5:35

SecurityFirstCorp
What Is Public Key Cryptography? - SecurityFirstCorp.com
6 months ago - 2:44

Social Media Trails
How Public-Key Cryptography Changed Our Digital World! #Shorts
1 year ago - 0:45

Neural Nexus
Public Key Cryptography: Unsung Hero of Internet #internet #cryptography #trending #shorts #short
10 months ago - 0:42

Fortris
How does public key cryptography work?
1 year ago - 1:32

TechTales
The Dawn of Digital Signature Technology
3 months ago - 0:52

FAME WORLD EDUCATIONAL HUB
#27 - Understanding Public Key Cryptography | Blockchain Tutorial @FAMEWORLDEDUCATIONALHUB
1 year ago - 4:34

TheCrimeReel
What Is The History Of Public-key Cryptography? - The Crime Reel
2 months ago - 3:23

Neural Nexus
Cryptography Origin #cryptography #new #trending #trendingshorts #shorts #short #video #viralvideo
10 months ago - 0:43

Neural Nexus
Steganography #cryptography #new #trending #trendingshorts #shorts #short #video #viralvideo #news
10 months ago - 0:42

Silicon Rovers
Cryptography for beginners | Why Cryptography | Symmetric vs Public Key Cryptography
4 years ago - 2:38

Crypto hunter
Understanding Elliptic Curve Cryptography in Bitcoin
2 months ago - 0:52

James Forsythe
How Will Public Key Cryptography Be Used In A U.S. CBDC System?
2 years ago - 0:58

James Forsythe
Why A U.S. CBDC System Would Use Public Key Cryptography
2 years ago - 0:21

हरीओम
public key cryptography | RSA
8 months ago - 6:23

Web3 Working Group
What Is Public Key Cryptography? #Short – See Full EP for more
2 years ago - 0:57

SDictionary
Public key cryptography Meaning
10 years ago - 0:36

BitnByte Mining
🔐 RSA Encryption Explained: Secure Data Transmission! 🌐💡 | Cryptography & Crypto Wallets 🔑#crypto
8 months ago - 0:58

Stevdza-San
Public-Key Cryptography Explained
1 year ago - 1:01

County Office Law
How Does Public Key Cryptography Work? - CountyOffice.org
1 year ago - 1:36

SDictionary
Public-key cryptography Meaning
10 years ago - 0:46

Ryan Riley
Introduction to Basic Cryptography: Public Key Cryptography
10 years ago - 16:50

SecurityFirstCorp
How Does Public-Key Cryptography Work? - SecurityFirstCorp.com
6 months ago - 2:44

CryptoBasics360
How Does Symmetric Cryptography Relate To Public Key Cryptography? - CryptoBasics360.com
4 weeks ago - 3:16

Course Grinder
Introduction to Public Key Cryptography
9 years ago - 8:26

Tech gyros
China's Quantum Leap: Breaking RSA Encryption! #quantumcomputing #tech
2 weeks ago - 0:48

CryptoBasics360
Public Key Cryptography Explained For Beginners? - CryptoBasics360.com
2 months ago - 3:26

Kenan Polat
The Role of Public Key Cryptography in Cryptocurrency Security
5 months ago - 0:41

Cloud Concepts
Public and Private Keys - Public Key Cryptography - SSH Keys - Public Key RSA Encryption Decryption
1 year ago - 3:32

Carizmian
Security Protocols (TLS), Public-Key Cryptography, X.509 & Certificate Issuance
2 years ago - 1:56

ByteQuest
Asymmetric Encryption Visually Explained #cybersecurity #shortsvideo
1 year ago - 0:44

Aaron Solt
Public-Key Cryptography Math Explained
10 years ago - 10:33

Geekus Maximus
P12 - Public-Key Cryptography Standards (PKCS) #12 - Security+
4 months ago - 0:39

Note creation
Difference between private key cryptography and public key cryptography
1 month ago - 2:03

Neural Nexus
Cryptography #cryptography #trending #trendingshorts #shorts #short #video #viralvideo #viralshort
10 months ago - 0:47

Dot by Dot
How Strangers Share Secrets in Public 🤯 | Diffie-Hellman Explained FAST
2 months ago - 0:27

MoneyMindset
Quantum Computing: The End of Crypto as We Know It? #shorts
4 months ago - 0:32
Wolfram U
Introduction to Cryptography: Public-Key Cryptography
1 year ago - 15:10

Amit Gupta
2104 Public Key Cryptography
4 years ago - 3:13

ProsperityPursuits
Quantum Computers: The Secret Threat to Public Key Cryptography
2 years ago - 0:19

Dereck Cram
Public-Key Cryptography Video
8 years ago - 2:12
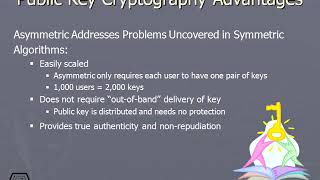
It Rating
299 Public Key Cryptography Advantages
5 years ago - 2:53

Code Sorcery
RSA - The Elegance of Public Key Cryptography
1 month ago - 8:50

Udacity
Public Key Cryptography - Applied Cryptography
10 years ago - 0:24

Prototype Project
DHKE multiplicative masking encryption/decryption
2 years ago - 1:01

Geekus Maximus
PKCS - Public Key Cryptography Standards - Security+
4 months ago - 0:37

TechKnowSurge
Foundations of Cryptography 2-9: Public-Key Cryptography
1 year ago - 11:18

AKSHARA CS
Introduction to Public Key Cryptography
4 years ago - 22:30

Datasafe World
Public-Key Cryptosystem, Public-Key Cryptography, Cybersecurity Mini Dictionary #shorts
1 year ago - 0:21

IT SPARC Cast
Public-Key Cryptography: The 1970s Breakthrough That Secures the Internet
3 months ago - 2:59

Ekeeda
Public Key Cryptography and its priciples | Cryptography and Network Security
3 years ago - 16:30

AB Labs
Asymmetric Key Encryption | Public Key Cryptography
5 years ago - 4:46

Science Traveller
Introduction to Public Key Cryptography Public Key Cryptography animation
6 years ago - 5:36

Dave
Private/Public Key Cryptography
8 years ago - 5:58

Zach Gollwitzer
A Crash Course in Public Key Cryptography (a.k.a. Asymmetric Cryptography)
5 years ago - 43:07

Hank Hackerson
CySec101 / EP.22 / Public Key Cryptography Intro / TryHackMe Cyber Security For Beginners
6 months ago - 1:06:03
Wolfram U
Introduction to Cryptography: Public-Key Cryptography
1 year ago - 15:10

DataSeed.org
C001M02L05 - Public Key Cryptography
7 years ago - 3:16
Hashcademy
What is the role of cryptography in blockchain? (Public Key Cryptography)
6 years ago - 1:28

Business Insider Nepal
Public Key Cryptography in simple #publickey #privatekey #cryptography#BBA check description #6thsem
1 year ago - 0:30

CryptoBasics360
What Are Examples Of Public Key Cryptography? - CryptoBasics360.com
2 months ago - 3:52

ChartCraftDayTrader
Demystifying Public Key Cryptography: The Key to Secure Communication and Cryptocurrency
2 years ago - 2:50

xkiller213
What is public-key cryptography?
13 years ago - 14:02

Spanning Tree
Diffie-Hellman Key Exchange: How to Share a Secret
1 year ago - 9:09

Mr. Rigden
A Very Brief Introduction to Public-key Cryptography
7 years ago - 6:54

Amir Moradi
Cryptography on Hardware - Session 11 - Public-Key Cryptography, Multipliers
3 months ago - 39:10

nirmal jeyaraj
Asymmetric or public key cryptography
8 years ago - 5:29

Amir Moradi
Cryptography on Hardware - Session 10 - Public-Key Cryptography, Adders
3 months ago - 42:43

DRP Türkiye
Elif Aslıcan Dişören - Public-key Cryptography
10 months ago - 16:25

CryptoBasics360
What Are The Limitations Of Public Key Cryptography? - CryptoBasics360.com
2 months ago - 3:06

Mayuri Amit
"The Knapsack Problem and Public Key Cryptography"
10 years ago - 3:21

MS Learning
Public Key Cryptography Explained Simply! #learnandgrow #proactivecybersecurity
5 months ago - 1:02

De Ceuster Academy
4.6.2 Discrete Math - Par 4.6: Public Key Cryptography
4 years ago - 10:23

U-tube
CEH19-6 Public key cryptography
5 years ago - 5:05































![[Cryptography6, Video 1] Public-Key Cryptography](/vi/SJ6qqhw4tjY/mqdefault.jpg)